Protecting Beyond DNS Flood & DDoS
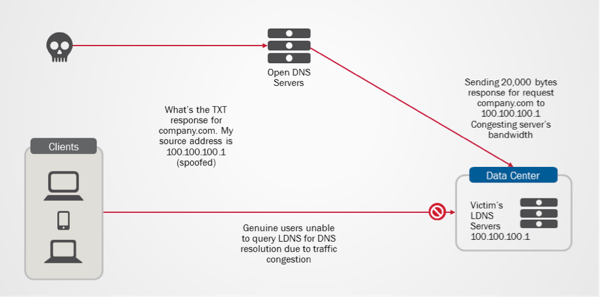
The recent slate of cyber-attacks involving DNS and NTP systems has again prompted questions about the comprehensiveness of DNS infrastructure’s security protection. Besides mitigating volumetric attacks such as DNS flood & DDoS, many organizations have realized the need for a more comprehensive DNS security protection, which helps in preventing DNS-related security frauds and non-volumetric based attacks such as amplification and cache poisoning attacks. On DNS Amplification & DNS Reflection Attacks You might concur that increasing DNS performance with adequate DNS rate limiting mechanism is probably one of the best approaches to tackle the problem of overwhelming DNS traffic and DNS DoS attacks. However, this does not address the issue of DNS Amplification and DNS reflection attacks, which has been made popular through the Spamhaus-Cyberbunker attack incident. In this incident, CyberBunker took the advantage of open DNS resolvers to launch DNS amplification attacks, causing Spamhaus to be unreachable at times. DNS amplification and reflection attacks are typically sent to DNS servers as legitimate DNS request, in hope to receive large data size responses. The huge data size responses will eventually use up all the available bandwidth causing congestion to genuine DNS queries and responses. As such, DNS query rate limiting mechanism and higher QPS performance will not be able to counter the attack since the attacks typically come in small numbers of DNS requests. One of the ways to limit such attacks is to filter the request based on query type. Typically, DNS amplification and reflection attacks will request for ‘TXT’ or ‘ANY’ Query Type which tends to return responses with significant data size. By applying bandwidth rate limit to these query type request and large-data-size query responses, we will be able to prevent bandwidth congestion caused by these attacks. Worried about the complexity of the bandwidth rate limiting solution? Well, it only takes less than 10 lines of iRules (shown as below) on F5 DNS platform to get this enforced and implemented. when DNS_REQUEST { if { ([DNS::question type] eq "TXT") } { rateclass dns_rate_shape } } when DNS_RESPONSE { if { ([DNS::len] value > 512) } { rateclass dns_rate_shape } } Diagram 1: DNS Reflection attacks blocking genuine users from accessing LDNS server. Cache Poisoning Attacks DNSSEC is poised as the eventual and ultimate solution to counter DNS cache poisoning attacks. Though the adoption rate of DNSSEC is encouraging, it takes all parties to deploy DNSSEC signing and validation to fully protect against cache poisoning. While waiting for DNSSEC adoption rate to mature, is there any interim solution to reduce or prevent cache poisoning attacks? Based on DNS RFC standards, name servers are required to treat domain names request with case-insensitivity. In other words, the names www.foo.com and WWW.FOO.COM should resolve to the same IP address. However, most name servers will preserve the original case when echoing back the domain name in the response. Hence, by randomly varying the case of characters in domain names queried, we will be able to add entropy to requests. With this verification mechanism, the name server response must match the exact upper and lower case of every character in the name string; for instance, wWw.f5.CoM or WwW.f5.COm, which significantly reduces the success rate of cache poisoning attacks. With F5’s DNS solution, this mechanism can be enabled with just a check box on the management pane. The packet capture of the query case randomization process by F5 DNS is shown as below. As depicted in the diagram, for queries to www.google.com, F5 Cache DNS will randomize the character case of the query prior sending the query to Google’s authoritative DNS server. This greatly reduces the chances of unsolicited queries matching the domain name and DNS request transaction ID, which causes the poisoning of cached DNS records. Diagram 2: Character case randomizer in F5 DNS solution dramatically reduces the possibilities of DNS cache poisoning attacks DNS is among the hoariest of internet services that is still widely used today. Its usage continues to grow due to its simplicity and proliferation of smart devices. Hence, it is truly important that proper solution design and architecture approach are being put in place to protect the infrastructure. After all, the protection investment might be only a fraction of what you are paying for during an attack.635Views0likes5CommentsSecurity is a process
A newspaper report recently warned that many IT products and applications, including payment systems, lack adequate security. The reasons cited are that firstly, security is treated as an afterthought, and secondly, because trained practitioners are not involved in the design and implementation. F5 views security as a process. It should be managed as such. There’s an important role for the security experts who build the policies that ensure security and compliance within the organization. And, there’s an equally important role for the programmers who develop the software. But the two are quite distinct from each other. Business applications are the critical assets of an enterprise. Its security should not be just left to the software engineers to decide because they are not security professionals. Therefore, the prudent approach is to offload the burden of coding security policies from the software programmers onto credible security solutions professionals. Viewed from that perspective, security is as an end-to-end process, with policies to govern the various areas wherever there is user interaction with the enterprise – device, access, network, application and storage. Given the complexities of the different moving parts, it sometimes makes sense to combine several of the point security concerns into a converged solution. In short, this is akin to process simplification not too different from what consultants would call “BPR" in the business world. However way, you see it, from a CFO perspective, this represents immense cost savings boh operationally as well as in capital costs. For example, when it comes to application security, the trend is to build it into the application delivery controllers. ADCs are designed to natively deliver applications securely to end users. In today’s context, ADCs act as secured gatekeepers to the applications; they prevent unauthorised access and are able to add-on capabilities to mitigate complex application level attacks such as those defined by OWASP. However, the situation is growing more complex. CIOs are increasingly faced with the task of balancing the needs of a younger, empowered and demanding Gen Y workforce who want the freedom to work from their device of choice as well as the ability to switch seamlessly between their social and enterprise networks. The CIO challenge is how to protect the company’s business assets in the face of increasing and more complex threats. Add to this the desire to leverage the cloud for cost control and scale and the security considerations can potentially spiral out of control. The situation calls for innovative security solutions that can understand the behaviour of enterprise applications as well as user behaviour, and be able to enforce corporate security policies effectively with minimum impact on user experience. F5 believes that security is a trust business. Having the right process and policies trumps choosing a vendor. It is the policies and process that determine the required solution, not vice versa. For a Japanese version of this post, please go here.305Views0likes0CommentsF5 Predicts: Internet of Things Drives Demand for ‘Social Intelligence’
‘Innovation distinguishes between a leader and a follower’, Steve Jobs once famously said. A saying that is crucial for organizations in their efforts to be a ‘global player’. There are currently lots of innovation areas in the technology space, spurred by the ‘Internet of Things’ (IoT). This trend is already being tapped in a broad variety of industries, such as enterprise and public sector in terms of smart roads or for sensor networks in building, on trains, hospitals, and in factories. The term ‘Internet of Things’ can be simply explained: It is a technology that enables real-time and accurate data sensing with the ability to wirelessly transmit data to other objects on the network. For instance, products that are being embedded with sensors enable a company to track movements of products and monitor any interactions. Having this data at hand provides decision makers the advantage to fine-tune their existing business models. But beyond business, IoT is getting to transform our personal lives too, according to Forrester’s Top 10 predictions for the Asia Pacific tech market in 2014. Sensors getting people fitter, finding keys, unlocking houses and monitoring ambient temperature, among many others. One of the things that comes along with the ‘Internet of Things’ is the increase in connections, inevitably giving rise to higher network traffic, thus stressing the existing network infrastructure. This requires an infrastructure that is scalable, flexible and more intelligent than ever before. Forrester analyst Michele Pelino stated recently that a key issue that needs to be worked out will be the development of an IoT ecosystem, before the technology can be widely adopted. The first challenge for enterprises, however, is that their current IT infrastructure may not be able to scale quickly enough to cater to the demands of the business. Secondly, as Pelino pointed out, there would need to be a tried and tested ecosystem of Independent Software Vendors who are able to take advantage of all the data from the various sources to provide analytical insights. Finally, the adoption of new technologies usually takes time due to policy and business changes. From a technology point of view, it will mean a dependence on data centers equipped with information processing tools like analytics engines, business intelligence software and more importantly, an intelligent application delivery infrastructure. While the analytics can provide the much-needed ‘social intelligence’ capability for the business to tap, the intelligent application delivery system can ensure that such insights are delivered on a real-time basis and securely to the end user. This need for real-time secured ‘social intelligence’ stems from the advent of IoT driven intelligence and creates the demand for a suite of application services. Eventually these insights need to reach the relevant decision makers – services that provide real-time traffic optimization, availability and security for data flowing through such business intelligence apps. Ultimately, these solutions need to manage such an infrastructure from a single point of management and this has lead to the birth of Software Defined Application Services (SDAS), the next phase in the lengthy evolution of application delivery. SDAS is the result of delivering highly flexible and programmatic application services from a unified, high-performance application service fabric. Orchestrated intelligently, SDAS can be provisioned to solve significant challenges from the whirling maelstrom of trends driving IT today. Ultimately, SDAS relies on abstraction; on the ability to take advantage of resources pooled from any combination of physical, virtual and cloud deployed platforms. All in all, IoT is a technology promising compelling benefits in our personal lives and business environments. Inevitably, back end technology will need to keep up with these developments and become ever more sophisticated in the era of the ‘Internet of Things’.300Views0likes0CommentsHTTPS的"S"不代表SSL
This is a localised version of the original articlehere. 當瀏覽器出現一個掛鎖圖像時,我們很自然的會假設該網站正使用SSL以確保我們的通訊安全。它同時也告知消費者該網站是安全的。根據CA Security Council的2015消費者信任調查,只有3%消費者會將他們的信用卡資訊提供給沒有掛鎖圖像的網站。 此種安全印象的影響性並不局限於消費者。F5最新的應用交付現狀調查報告顯示,已經或有計畫建置"SSL Everywhere"的受訪者表示,對於他們企業承受應用層攻擊的能力比較有信心,在1到5的信心評分中獲得3或更高的評價。 事實是,大多數人無法告訴你SSL代表什麼意義,更別說是描述它的運作方式。他們只知道那是一種確保應用或網站交易,包含潛在的機密資訊的安全機制。 那有一部分是科技專有名詞描述的錯。我們用SSL來描述協定(RFC 6101),以及作為描述一個安全連接的通稱。SSL是安全性的通稱,就好像Google是搜索引擎或者舒潔是衛生紙的代名詞一樣。 實際上,HTTPS並不是真的需要SSL。HTTPS的"S"代表安全(secure),而且它只簡單的要求提供確保二個端點,例如一個瀏覽器和一個Web網站之間安全連接的方法。而且,越來越明顯的是,其所代表的意義事實上是指在TLS協定(而非SSL)之上的HTTP。 這是一個很重要的區別,因為儘管它們有著相同的根源,但TLS並不是SSL,SSL也不是TLS。它們是不同的協定,各有它們本身獨特的挑戰、問題和衝擊效應。二者都是以相同的方式確保安全連接 - 它們使用安全憑證以進行認證,以及使用公鑰/私鑰加密 - 然而雙方仍存在著建置上的差異性。 我們為何要關注這件事?你應該在意,因為最新的Web應用協定HTTP/2和SPDY並不支援SSL。它們支援的是TLS。它們本身並沒有這樣的要求,不過支援這二項協定的瀏覽器只能在TLS(而非SSL )之上提供該項支援。 必須承認的是,今天使用HTTP/2或SPDY的網站並不多,但數量正在成長。在W3CTech (July 2015)報導中指出,新的HTTP/2標準已於2015年5月發行最終版,現在獲得所有網站的0.4% (高於7月初的0.24%)以及頂尖1000網站的7.5% 採用。也就是說頂尖的1000網站中,現在有7.5% 藉由HTTP/2提供內容服務。 我們談論的並不是只局限於瀏覽器和伺服器。我們同時也必須思考在整合上所代表的意義,當使用頂尖1000網站的一些API時,或許會被迫非僅採用HTTP/2或SPDY,而且也包括TLS 。Google所有公共服務的加密都是使用TLS。如果你要整合Google的一些功能,就應注意他們使用的是TLS而非SSL。因為這有著實質上的差異。 另外還必須注意的是它涉及到商業上一些盤根錯節的問題。在支付卡產業(PCI)標準規範下,SSL在2016年6月30日之後不得繼續使用。那個時間點之後,將明確要求採用TLS。這意謂著必須做一些改變以維持遵循PCI。當然,你會做相應的配合,因為如果不遵循標準的話將面對很多複雜的挑戰。例如,信用卡發行者會要求較高的商家帳戶費用和罰鍰,或者完全取消你的支付與交易處理資格。如果發生權利侵害事件,你的公司將因為未能在安全性上做到正當注意調查(due diligence)而面對較高的法律訴訟與罰責風險。 當然,如果說期望你此刻就要從SSL轉移到TLS,也是不實際的。畢竟,雖然TLS是以SSL v3為基礎,但它並非100% 向下相容,而且需要做一些組態變更才能取消SSL以迫使使用TLS。組態變更通常需要進行一次重新啟動。對一個大規模環境而言,這個程序必然會造成服務中斷而且耗費時間。 不過,現在正是開始認真考慮的時刻,你必須決定還要支援SSL多久以及何時要轉移到純正的TLS。290Views0likes0CommentsDNS Protection and Performance, Have Both!
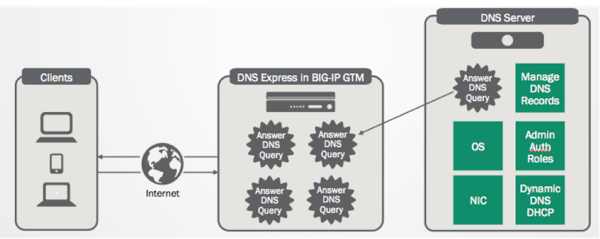
There has never been a better time to cripple the Internet by exploiting the vulnerabilities of DNS systems. The proliferation of mobile devices coupled with vulnerabilities of open source DNS systems is keeping a lot of organizations awake at night, amongst them, the large enterprises, financial services institutions and carrier service providers. Existing firewalls were insufficient to protect DNS infrastructure from the fast-evolving attacks. To counter the attacks and to enhance security protections, proven solution architecture and comprehensive design considerations ought to be put in place for DNS infrastructure. Let’s discuss further on the solution design considerations for a more secured DNS infrastructure. Performance vs. Traffic Analysis There are generally two schools of thoughts on how we should counter the overwhelming DNS attacks – by increasing protection through traffic analysis and packet inspection or by increasing the DNS performance. Both approaches are resource intensive and require heavy investment. Prior to the massive growth of mobile devices, open source DNS systems such as BIND were able to cope with the DNS traffic and pockets of attacks. The recent upswing of mobility trend has multiplied the DNS traffic by tens-of-fold, leaving DNS systems extremely vulnerable to even small-scale attacks. For the camp who advocated for stronger security through packet inspection and analysis on DNS traffic, the process is resource intensive and ineffective as IP addresses for UDP traffic can be easily spoofed. The inspection process will also create higher latency for DNS responses. Despite implementation of resource intensive packet inspection mechanism, the low query response rate (~30K QPS per instance) of BIND - the open source DNS systems is deemed to be the Achilles heel of a well-protected DNS system. Based on various sharing from enterprises and carrier service providers, overwhelming DNS traffic with mixed and spoofed IP addresses can easily kill their DNS infrastructure. Personally, I am more inclined to the latter approach. The latter approach of increasing DNS performance for better security argues that non-malicious DNS request should be responded regardless of their genuinity. Instead of utilizing computing resources for packet analysis, the resource can be put into better use by improving the DNS query response rate. With F5’s DNS Express patented technology, DNS records will be stored in memory (RAM) and queries are responded at higher speeds. This increases the DNS performance dramatically and allows F5 VIPRION to support up to 10 million queries per second on a single hardware platform. The high performance DNS platform hence serves as a deterrent and effective protection against DNS DoS and spam attacks. So, let’s rethink about the DNS operation team’s mission for a second, isn’t that to keep DNS alive at all times? Diagram 1: F5 DNS Express offloads the DNS servers from answering query responses, hiding Controller DNS Servers from DoS and other attacks Security attacks and its counter measures are ever-lasting battles which require innovation and proper solution design to stay ahead of the game. In my subsequent posts, I will share more about countering Cache Poisoning attacks and DNS Amplification/Reflection attacks. Stay tuned.264Views0likes0CommentsWho needs a Bot Army these days?
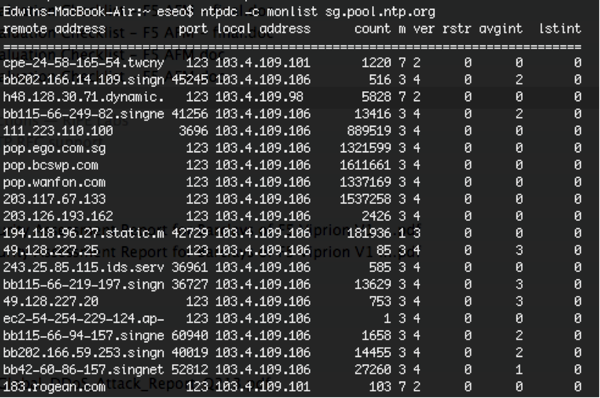
It’s been a while - a long while - since I last (officially) blogged. Too many distractions with a new role, new travels, and a new family member - sucks away the creative juices. Alas, sitting at an airport lounge after a 3 city Security Roadshow in Bombay/Delhi/Bangalore brings out the adrenaline rush of blogging once more. I’ve been evangelizing the need for DoS protection for quite a while. Events of last year (2013), and even the beginning of 2014, have made my job easier (Happy New Year!). I used to equate DoS (rather Distributed DoS) attacks with Bot Armies - kinda like the Orcs that we saw in the LOTR (Lord of the Rings**) saga. The Bots (Orcs) still exist - but seems like the Bot Herder (I’ll call him “Sauron” **) is summoning a new type of Army these days - a new generation of orcs used to carry out his mission to wipe a particular service/server from the face of the Internet world - You and Me! Yes - US! Who needs a Bot Army these days? There are gazillions of Internet users and servers out there. There isn’t a need for any kind of endpoint infection/malware. That would be troublesome. All you need is an unsuspecting (and poorly protected) + popular web server, and some programming flair with JavaScript (JS) or iFrames. Then you need to compromise that popular web server and input the malicious JS/iFrame into the landing web page. So when a user visits this compromised popular website (e.g. an online gossip portal) to read about the latest Hollywood gossips, the hidden JavaScripts or iFrames gets executed within his browser and causes him to send multiple GET requests to the victim. And the victim gets hoarded with a torrent of GET requests, and if its not sufficiently and appropriately protected, guess what happens? Bam! 2014 began with an interesting new type of attack against a couple of gaming sites like League of Legends, Steam and Battle.net using yet another type of “botnet”, except that these weren’t bots but actual Network Time Protocol (NTP) servers. The NTP protocol is used by many servers and endpoints to sync system clocks - for example my mac uses time.asia.apple.com. Leveraging the inherent “trust” that the UDP protocol exhibits (aka stateless), and a relatively forgotten command called “monlist”, this is how it works. From my laptop, a small query of 234bytes returns a response of 100 packets each of 482bytes, producing an amplification factor of approximately 205x (you get the hint). So I need to be armed with a list of open and unpatched NTP servers (which isn’t difficult to find - there are automated programs out there that can “assist"), and spoof the IP address of someone whom I don’t like, and shazam. An example of the now infamous “monlist” command for an unpatched NTP server looks like: This reminds me of the DNS Reflective Amplification attacks during the Cyberbunker-Spamhaus saga in March of last year (2013). Again, the trust model of the DNS protocol was exploited, and what that didn’t help with the problem were those 20-something million open DNS resolvers which neither perform any kind of filtering nor any request verification or traffic management of DNS responses. And as a result, 300Gbps of DNS responses towards an unsuspecting victim, which even caused collateral damage to International Peering exchanges. Now, how do we deal with these? For the DNS and NTP reflective amplification attacks, apart from deciding to not be an open DNS resolver, or disabling the “monlist” command, if you are a service or hosting provider to one of these potential “Orcs”, one simple way is to monitor the outbound BPS/PPS/Number of connections originating from the server. When it gets anomalously high, move to the next step of monitoring perhaps the Top 10 destinations these guys are sending towards. It doesn’t make sense that a DNS server out there is sending 1M DNS “Any” responses per second to www.f5.com. Apply an appropriate rate shaping policy as needed and that will help protect your own network infrastructure, save some peering/transit costs, and help the poor victim. The HTTP reflection attack is a bit more challenging, given that as mentioned previously - it isREALHTTP traffic fromREALbrowsers out there. You can’t filter based on malformed HTTP packets. You can’t filter based on URL since it’s typically a legitimate URL. This calls for Anti-Bot Intelligence, like: TCP SYN Cookie verification (L4) HTTP Redirection verification (L7) JavaScript / HTTP Cookie verification (L7) CAPTCHA verification (L7) With the ability to step-up countermeasures dynamically and when needed. Of course, the latter verification methods are higher in the OSI stack (Layer 7), more advanced and computationally more expensive to perform. Here at F5, we’ve found that (3) and (4) have been extremely effective in terms of combating DoS tools/scripts and even the hidden JavaScripts/iFrames mentioned above. These guys typically bail out when it comes to solving complex JavaScript puzzles or checking of mouse/keyboard movements etc., and not to mention solving CAPTCHA puzzles. Once this happens, throw the errant source into a penalty box for a period of time, then repeat the rinse and lather. Dynamically increase this penalty box timeout when the errant source fails multiple times. This will effectively thwart any attempt from the errant source in sending HTTP requests to the victim server. Lastly, work with your upstream service provider, or engage a cloud-based anti-ddos service when the attacks become too large to handle. Sound the SOS! It is common-sense the only possible way to mitigate 300Gbps floods is in the service provider cloud / cloud-based anti-ddos service, likely using a distributed scrubbing “anycast” model, where each distributed scrubbing center sucks in the traffic destined for the victim like a big washing machine and starts cleaning. That said, there are many ways to skin a cat - likewise, there are many ways to solve a DoS problem. Pay particular attention to attacks as they move up the OSI stack toward Layer 7. These are typically harder to mitigate, but fortunately not for F5. So if you’re thinking that botnet armies are the Sole source of menace in the DoS world out there, they’re not. Everyday Internet users like you and me could be an unsuspecting participant in the world’s largest DoS to be. ** Source: The Lord of the Rings, J.R.R Tolkien, 1954261Views0likes0CommentsAPAC market research points to WAF being integrated with application delivery
We entered 2014 on a fillip. Frost & Sullivan had just named us the vendor leading WAF market in Asia Pacific and Japan. The Frost Industry Quotient, put F5 and nine other companies under their analytical magnifying glass, examining our market performance for CY 2012 as well as key business strategies. They left no strategy unturned it would seem. Product and service strategy, people and skills strategy, business and even the ecosystem strategy were all held up to scrutiny. But the real scoop wasn’t that we were No 1 but that Frost IQ had discerned developments in the market that point towards WAF being integrated with application delivery. The researchers noted that the convergence would lead to a more intelligent and holistic way for organizations to protect their web applications. The market is validating what we said a year ago when we launched BIG-IP Advanced firewall Manager, the first in the industry to unify a network firewall with traffic management, application security, user access management and DNS security capabilities within an intelligent services framework. Every day, publicly known or otherwise, organizations grapple with attacks that target their applications in addition to those that threaten the network. Because F5 solutions occupy strategic points of control within the infrastructure, they are ideally suited to combine traditional application delivery with firewall capabilities and other advanced security services. The bell tolls for the traditional firewall. Eventually it will be replaced by intelligent security. F5’s integrated approach to security is key in mitigating DDoS attacks, helping to identify malicious actions, prioritize how requests from specific locations are handled and focus on addressing properly qualified requests. Enabling security services on our ADCs makes it possible to consolidate multiple security appliances into one single device. This consolidation includes a WAF that analyses traffic and can propose rules to automatically protect the enterprise. I caught up quickly with Christian Hentschel, SVP Asia Pacific and Japan, on his views of the new accolade. Aside from being very proud to be recognized as the leading WAF vendor in APJ, a testimony of our strategy and the team’s focus, he noted that customers view traditional firewall less relevant with the sophistication in cyber-attacks on layer 4-7 today.248Views0likes0CommentsIT security isn’t one size fits all
The security landscape today is highly complex, which can largely be attributed to the increasingly sophisticated nature of cyber attacks, particularly from an execution perspective. For example, DDoS attacks are now reaching speeds of up to 400Gbps, targeting both the network and application layer. Evidently, attackers are progressing towards other methods to bypass traditionalsecurity defenses, including the firewall. In this particular scenario, the challenge for organisations with application-layer DDoS attacks is to differentiate human traffic from bot traffic. In addition, the motivation behind attacks is becoming more complex especially from a political and economic standpoint. The NSA leaks by Edward Snowden, which revealed classified information from governments including the US, UK, Australia, Canada, and New Zealand is a recent example of a high profile hacking incident that certainly reminds us of this fact. Moreover, one of the biggest threats to IT security is now organsied cyber theft and fraud, as the smartest criminals in the world are increasingly realising the substantial financial gains that can be made via online crime. Hence, the need for an enterprise to ensure it is adequately protected against cyber attacks is becoming increasingly critical. An effective security strategy will cover all devices, applications and networks accessed by employees, beyond the enterprise infrastructure itself. Traditional security methods such as next generation firewalls and reactive security measures are losing the fight of being effective against the new breed of attacks. Security is now very much about the protection of the application, enforcement of encryption and the protection of the users identity, and less about the supporting network infrastructure. This is because it has become far less static in recent times and has truly proven to be nothing more of a commodity transport vehicle for the complex applications that run on top of it. What organisations need is a security strategy that is flexible and comprehensive, with the ability to combine DNS security and DDoS protection, network firewall, access management, and application security with intelligent traffic management. Developments in the market which has seen theintegration of WebApplication Firewalls (WAFs) with Application Delivery Controller (ADC) platforms, as recognised by a recent study by Frost & Sullivan (the Frost Industry Quotient), has driven F5 to create a new vision / architecture called F5 Synthesis for the application delivery market. This vision offers a high performance network fabric to protect fundamental elements of an application (network, DNS, SSL, HTTP) against sophisticated DDoS attacks. F5 Synthesis, through the use of tested reference architectures, ensures that applications are kept secure and available as customers make the journey toward software defined data centres (SDDS). Moreover, F5’s DDoS protection solution delivers the most comprehensive attack protection available on the market to date. While the average DDoS attacks reach 2.64 Gbps, upgrades to F5’s BIG-IP platform allow servers to handle attacks as large as 470 Gbps. Not only is there enough bandwidth to mitigate a DDoS attack, the extra capacity allows online companies to continue normal business - even while under attack. Security won’t be one size fits all during 2014. End users will expect high performance, however organisations must ensure they deploy security solutions that don’t become a bottleneck. This year, we can expect to see a rise in a multi-dimensional or 'cocktail' style attacks: DDoS attacks combined with application layer attacks and SQL vulnerabilities. As such, the traditional firewall is no longer a viable security defense, and organisations need to have a multi-stack security approach, combined with a process to handle internal control. With attacks from multiple angles on different devices, single-purpose security machines will be phased out in favour of sophisticated multi-purpose machines.238Views0likes0CommentsF5 predicts: IT departments to become brokers
IT brokers In this rapidly evolving age of technology, business demands are constantly changing. New technology innovations are introduced into the market at a dizzying rate. IT departments have the core role of providing technology solutions for business problems within organizations. However, instead of delivering these solutions themselves, IT departments of tomorrow will deliver solutions by managing relationships with multiple third-party IT innovators. This is to ensure the latest technology; a wider depth of technical expertise, as well as higher efficiency and allocation of manpower resources internally. To understand this shift in roles and relationships, we first examine how third-party IT innovations have helped businesses meet the changing demands of the current age with cloud and security solutions, and the various benefits of maintaining relationships with third-party IT innovators. Third-party innovations to meet changing business demands Robust third-party technological solutions are valued above all, for these bring a drastic increase in efficiency, productivity, agility and more importantly, competitive advantage. Cloud Solutions A 2012 study by the IBM Institute for Business Value and Economist Intelligence Unit, which surveyed 572 business and technology executives across the world, found that 90% expect to have implemented cloud in their organizations in the next three years. This brings the expected growth now to 41% from 13% at the time of the study. In this digital age, consumers have drastically changed their browsing and purchasing behavior. According to research by Gartner, it is predicted that more than 7 billion people and businesses, and at least 30 billion devices will be online by 2020 — which means most of the world will communicate and transact in the online sphere. To cope with this change, businesses have to adapt their strategies accordingly — i.e. find more efficient ways to conduct processes, share and exchange information, reach consumers and at the same time, ensure these transactions are accomplished in a secure environment. An example of an organization that has reworked its business model with a cloud computing solution is Etsy, a widely used online marketplace for handmade goods. Etsy “is able to cost-effectively analyze data from the approximately one billion monthly views of its Web site and use the information to create product recommendations.” (Forbes, 2012) According to research by Gartner, in 2015, “at least 20% of all cloud services will be consumed via internal or external cloud service brokerages, rather than directly, up from less than 5% today”. While the debate has mostly revolved around internal (private) and external (public) cloud models, it seems like the hybrid model may be a more viable solution amongst businesses concerned primarily with security. For example, Action for Children works with about 50,000 children and young adults in more than 600 projects worldwide. The organization needed to keep sensitive data in-house, and at the same time, manage web traffic and conduct data analysis for a deeper understanding of their customers for fundraising activities. They achieved this through a hybrid cloud solution. Security Solutions “Through 2015, mitigating data breaches will cost 10 times more than installing data protection mechanisms on mobile devices.” Gartner, November 2010 Security has become critical aspect of the digital age and will require the know-how of third-party service providers. The adoption of solutions from multiple parties, coupled with vast amounts of information shared and transacted online between and among service providers and organizations require security solutions to shield sensitive data. Organization networks today are subject to targeted attacks and intrusions. Denial-of-Service (DOS) attacks for example, can knock out critical applications, which in turn affects both businesses and its customers. Hackers are also constantly evolving their attack vectors. This online battlefield can prove bewildering to the IT department. Third-party service providers offer both expertise and robust infrastructures to ensure the protection and availability of organization’s networks. The advantages of brokerage There are multiple plus-points to IT departments forging and maintaining relationships with third-party service providers. These relationships can be put in place through various contractual agreements, including Service Level Agreements (SLAs). First, service providers are equipped with all the new technologies available and most applicable for use in the organization, as well as the knowledge of best practices within the industry. IT departments can therefore avail itself to the best technology fit for its organization. IT departments can also better manage and deploy their internal manpower. IT departments have been accused of being ‘disconnected’ from the business. In this way, IT staff can be devoted to understanding the business and propose the best technology from its service providers. This model will also make it easier for the IT department to demonstrate value, as they will be able to reduce and manage cost and measure productivity. Furthermore, this can be done at a faster pace. Days when enterprise application implementation took 1 to 2 years will remain in the pass. IT departments can move from a cost center to being a cost controller. The role of IT departments in businesses is continuing to evolve more in light of changing consumer demands. The full realisation of this has yet to be seen, but we look forward to what’s yet to come.227Views0likes0CommentsTackling Cyber Attacks From Within
An increasing number of organizations face serious security threats that are socially, politically and economically motivated. Conventional firewalls are no longer enough to prevent complex and frequent cyber attacks such as multi-layer distributed denial-of-service (DDoS)/application layer attacks and SQL injection vulnerabilities. In the past year, the number of DDoS attacks targeting vulnerable spots in web applications has risen and attackers are using increasingly complicated methods to bypass defenses. Meanwhile, 75% of CISOs aware external attacks had increased – 70% of CISOs noticed that web applications represent an area of risk higher than the network infrastructure. The challenge with application-layer attacks is to differentiate human traffic from bot traffic. DDoS mitigation providers frequently utilize browser fingerprinting techniques like cookie tests and JavaScript tests to verify if requests are coming from real browsers. However, most recently, it’s become apparent that cybercriminals have launched DDoS attacks from hidden, but real browser instances running on infected computers. This type of complex cyber attack is incredibly hard to detect. What organizations need is a security strategy that is flexible and comprehensive, much like F5’s web application firewall (WAF) and security solution. F5 recently received the 2013 Frost & Sullivan Asia Pacific Web Application Firewall Market Share Leadership Award. This recognition demonstrates excellence in capturing the highest market share for WAF solutions in the region and its achievement in remarkable year-on-year revenue growth – a true testimony to the execution of F5’s security strategy. Christian Hentschel, (SVP, APJ) noted that cyber-attacks often result in the loss or theft of intellectual property, money, sensitive corporate information, and identity. An effective security strategy encompasses not only the enterprise infrastructure but also the devices, the applications, and even the networks through which users access mobile and web applications. F5’s ICSA-certified WAF and policy-based web application security address cyber-threats at the application level. In September 2013, F5 strengthened its security portfolio with the acquisition of Versafe Ltd. – a web anti-fraud, anti-phishing, and anti-malware solutions provider. The acquisition reinforces F5’s commitment to provide organizations with holistic, secure access to data and applications any time, from any device. F5’s comprehensive security solutions combine DNS security and DDoS protection, network firewall, access management, and application security with intelligent traffic management. Its flexibility to provide WAF both as a standalone solution and as an integrated offering on its BIG-IP® Application Delivery Controller platform provides customers with options that best suit their businesses. F5’s ability to provide end-to-end application protection, advanced monitoring, and centralized management without comprising performance make their WAF solutions the number one choice throughout the Asia Pacific region.221Views0likes0Comments