Implementing SSL Orchestrator - High Level Considerations
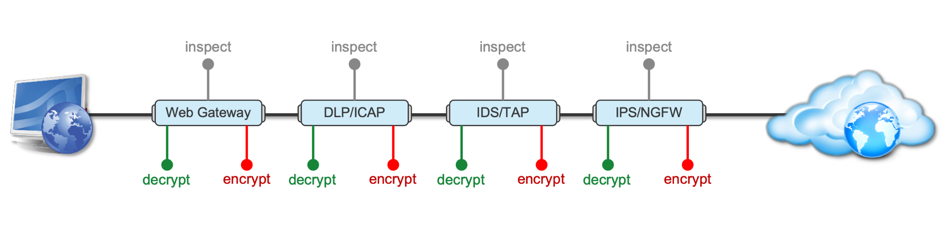
Introduction This article is the beginning of a multi-part series on implementing BIG-IP SSL Orchestrator. It includes high availability and central management with BIG-IQ. Implementing SSL/TLS Decryption is not a trivial task. There are many factors to keep in mind and account for, from the network topology and insertion point, to SSL/TLS keyrings, certificates, ciphersuites and on and on. This article focuses on pre-deployment tasks and preparations for SSL Orchestrator. This article is divided into the following high level sections: Solution Overview Customer Use Case Architecture & Network Topology Please forgive me for using SSL and TLS interchangeably in this article. Software versions used in this article: BIG-IP Version: 14.1.2 SSL Orchestrator Version: 5.5 BIG-IQ Version: 7.0.1 Solution Overview Data transiting between clients (PCs, tablets, phones etc.) and servers is predominantly encrypted with Secure Socket Layer (SSL) and its evolution Transport Layer Security (TLS)(ref. Google Transparency Report). Pervasive encryption means that threats are now predominantly hidden and invisible to security inspection unless traffic is decrypted.The decryption and encryption of data by different devices performing security functions potentially adds overhead and latency.The picture below shows a traditional chaining of security inspection devices such as a filtering web gateway, a data loss prevention (DLP) tool, and intrusion detection system (IDS) and next generation firewall (NGFW). Also, TLS/SSL operations are computationally intensive and stress the security devices’ resources.This leads to a sub-optimal usage of resource where compute time is used to encrypt/decrypt and not inspect. F5’s BIG-IP SSL Orchestrator offers a solution to optimize resource utilization, remove latency, and add resilience to the security inspection infrastructure. F5 SSL Orchestrator ensures encrypted traffic can be decrypted, inspected by security controls, then re-encrypted—delivering enhanced visibility to mitigate threats traversing the network. As a result, you can maximize your security services investment for malware, data loss prevention (DLP), ransomware, and next-generation firewalls (NGFW), thereby preventing inbound and outbound threats, including exploitation, callback, and data exfiltration. The SSL Orchestrator decrypts the traffic and forwards unencrypted traffic to the different security devices for inspection leveraging its optimized and hardware-accelerated SSL/TLS stack.As shown below the BIG-IP SSL Orchestrator classifies traffic and selectively decrypts traffic.It then forwards it to the appropriate security functions for inspection.Finally, once duly inspected the traffic is encrypted and sent on its way to the resource the client is accessing. Deploying F5 and inline security tools together has the following benefits: Traffic Distribution for load sharing Improve the scalability of inline security by distributing the traffic across multiple Security appliances, allowing them to share the load and inspect more traffic. Agile Deployment Add, remove, and/or upgrade Security appliances without disrupting network traffic; converting Security appliances from out-of-band monitoring to inline inspection on the fly without rewiring. Customer Use Case This document focuses on the implementation of BIG-IP SSL Orchestrator to process SSL/TLS encrypted traffic and forward it to a security inspection/enforcement devices. The decryption and forwarding behavior are determined by the security policy. This ensures that only targeted traffic is decrypted in compliance with corporate and regulator policy, data privacy requirements, and other relevant factors. The configuration supports encrypted traffic that originates from within the data center or the corporate network.It also supports traffic originating from clients outside of the security perimeter accessing resources inside the corporate network or demilitarized zone (DMZ) as depicted below. The decrypted traffic transits through different inspection devices for inbound and outbound traffic. As an example, inbound traffic is decrypted and processed by F5’s Advanced Web Application Firewall (F5 Advanced WAF) as shown below. *Can be encrypted or cleartext as needed As an example, outbound traffic is decrypted and sent to a next generation firewall (NGFW) for inspection as shown in the diagram below. The BIG-IP SSL Orchestrator solution offers 5 different configuration templates. The following topologies are discussed in Network Insertion Use Cases. L2 Outbound L2 Inbound L3 Outbound L3 Inbound L3 Explicit Proxy Existing Application In the use case described herein, the BIG-IP is inserted as layer 3 (L3) network device and is configured with an L3 Outbound Topology. Architecture & Network Topology The assumption is that, prior to the insertion of BIG-IP SSL Orchestrator into the network (in a brownfield environment), the network looks like the one depicted below.It is understood that actual networks will vary, that IP addressing, L2 and L3 connectivity will differ, however, this is deemed to be a representative setup. Note: All IP addressing in this document is provided as examples only.Private IP addressing (RFC 1918) is used as in most corporate environments. Note: the management network is not depicted in the picture above.Further discussion about management and visibility is the subject of Centralized Management below. The following is a description of the different reference points shown in the diagram above. a.This is the connection of the border routers that connect to the internet and other WAN and private links. Typically, private IP addressing space is used from the border routers to the firewalls. b.The border switching connects to the corporate/infrastructure firewall.Resilience is built into this switching layer by implementing 2 link aggregates (LAG or Port Channel ®). c.The “demilitarized zone”(DMZ) switches are connected to the firewall.The DMZ network hosts application that are accessible from untrusted networks such as the Internet. d.Application server connect into the DMZ switch fabric. e.Firewalls connect into the switch fabric.Typically core and distribution infrastructure switching will provide L2 and L3 switching to the enterprise (in some case there may be additional L3 routing for larger enterprises/entities that require dynamic routing and other advanced L3 services. f.The connection between the core and distribution layers are represented by a bus on the figure above because the actual connection schema is too intricate to picture.The writer has taken the liberty of drawing a simplified representation.Switches actually interconnect with a mixture of link aggregation and provide differentiated switching using virtualization (e.g. VLAN tagging, 802.1q), and possibly further frame/packet encapsulation (e.g. QinQ, VxLAN). g.The core and distribution switching are used to create 2 broadcast domains. One is the client network, and the other is the internal application network. h.The internal applications are connected to their own subnet. The BIG-IP SSL Orchestrator solution is implemented as depicted below. In the diagram above, new network connections are depicted in orange (vs. blue for existing connections).Similarly to the diagram showing the original network, the switching for the DMZ is depicted using a bus representation to keep the diagram simple. The following discusses the different reference points in the diagram above: a.The BIG-IP SSL Orchestrator is connected to the core switching infrastructure A new VLAN and network are created on the core switching infrastructure to connect to the firewalls (North) to the BIG-IP SSL Orchestrator devices. b.The client network (South) is connected to the BIG-IP via a second VLAN and network. c.The SSL Orchestrator devices are connected to a newly created inspection network.This network is kept separate from the rest of the infrastructure as client traffic transits through the inspection devices unencrypted.As an example, Web Application Firewalls (BIG-IP ASM) are used to filter inbound traffic. d. The LAN configuration for the connection to the BIG-IP ASM is as depicted below. e. The NGFW is connected to the INSPECTION switching network in such a manner that traffic traverses it when the BIG-IP SSL Orchestrator is configured to push traffic for inspection. Summary This article should be a good starting point for planning your initial SSL Orchestrator deployment. We covered the solution overview and use cases. The network topology and architecture was explained with the help of diagrams. Next Steps Click Next to proceed to the next article in the series4.4KViews7likes4CommentsImplementing SSL Orchestrator with OPSWAT MetaDefender
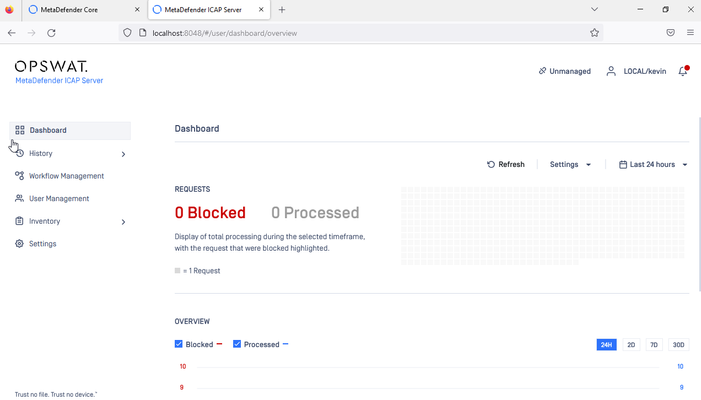
Introduction The Secure Sockets Layer (SSL) protocol and its successor, Transport Layer Security (TLS), are being widely adopted by organizations to secure IP communications. While SSL/TLS provides data privacy and secure communications, it also creates challenges to inspection devices in the security stack. What if attackers are hiding malware inside the encrypted traffic? An integrated F5 and OPSWAT MetaDefender solution solves the SSL/TLS challenges. F5 BIG-IP SSL Orchestrator centralizes SSL/TLS inspection. The decrypted traffic is then inspected by one or more OPSWAT MetaDefender ICAP Servers, which can prevent previously hidden threats and block zero-day exploits. This solution eliminates the blind spots introduced by SSL/TLS. This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. A video demo of this integration is available HERE OPSWAT MetaDefender Configuration Install and configure: OPSWAT MetaDefender Core OPSWAT MetaDefender ICAP Server Refer to OPSWAT Product Documentation for detailed instructions: OPSWAT MetaDefender Core OPSWAT MetaDefender ICAP Server When done your Dashboard should look something like this: BIG-IP SSL Orchestrator Configuration An OPSWAT MetaDefender ICAP Server is configured as an ICAP Server Service in BIG-IP SSL Orchestrator. BIG-IP SSL Orchestrator steers the decrypted web traffic through the OPSWAT ICAP Server(s), which are part of one or more Service Chains. Create the OPSWAT MetaDefender Service Under Services, click Add Service. In the service catalog, double click OPSWAT MetaDefender ICAP service. (If the version of BIG-IP SSL Orchestrator you’re using doesn’t have this option, then use the generic ICAP service.) This option is available from the ICAP tab in newer versions. Give it a name, OPSWAT in this example. Under ICAP Devices click Add. Enter the IP address of the MetaData ICAP Server, 10.1.60.4 in this example. Click Done. Specify the URI Path for Request and Response Modification. Click Save and Next at the bottom. From the Services Chain List select the Chain you want to add OPSWAT to, Services_Chain in this example. Move OPSWAT to the Selected field Click Save when done Deploy when done Testing the Configuration To check that you configuration is working as expected try to download an eicar testfile over HTTPS here. If everything was setup properly you should see a blocking page similar to this: Conclusion This completes configuration of BIG-IP SSL Orchestrator with OPSWAT MetaDefender. At this point traffic that flows through SSL orchestrator will be decrypted and sent to the OPSWAT ICAP Service and inspected for malicious payloads.854Views4likes0CommentsIntegrating SSL Orchestrator with McAfee Web Gateway-Transparent Proxy
Introduction SSL Orchestrator centralizes & manages decryption of SSL/TLS traffic. This enables security and monitoring tools to view the decrypted content and analyze it for threats and other anomalies. SSL Orchestrator removes the burden of decrypting content from your security tools so they perform better and are more scalable. An integrated F5 and McAfee Web Gateway solution eliminates the blind spots introduced by SSL/TLS encrypted content. Versions Tested This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 SSL Orchestrator version 11.0 McAfee Web Gateway version 11.2 McAfee Web Gateway will be configured as a Transparent Proxy Additional Help If setting up SSL Orchestrator for the first time refer to theF5 SSL Orchestrator Deployment Guides For information on SSL Certificate considerations and trust, refer to Implementing SSL Orchestrator - Certificate Consid... - DevCentral McAfee Web Gateway (MWG) Configuration Configure the Transparent Web Proxy as follows and click the plus sign under Port Redirects Set the Destination proxy port to 80 and click OK Click Save Changes Configure the Network Interfaces as follows Specify the IP address and mask to be used for eth2, 10.0.0.55 255.255.255.0 in this example. Specify the IP address and mask to be used for eth3, 10.1.1.5 255.255.255.0 in this example. The Default Gateway will be a Self IP address on SSL Orchestrator, 10.1.1.1 in this example. BIG-IP SSL Orchestrator Configuration The BIG-IP VLAN settings should look like the following 10.0.0.0 is the interface used for Transparent Proxy connections to the MWG 10.1.1.0 is the interface used for Transparent Proxy connections to SSL Orchestrator North_vlan is used for network connectivity from the BIG-IP to the North South_vlan is used for network connectivity from the BIG-IP to the South The BIG-IP Self IPs setting should look like the following 10.0.0.1 will be used for Transparent Proxy connections to the McAfee Web Gateway 10.1.1.1 will be used for Transparent Proxy connections from the McAfee Web Gateway Note: in this example SSL Orchestrator is deployed with an L3 Outbound Topology. That’s what the other two Self IPs are for. Your configuration will look different if using an L2 Topology. This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration Create the McAfee Web Gateway Service Under Services, click Add. In the Service Catalog select the Inline HTTP tab then double click on McAfee Web Gateway HTTP Proxy. Give it a name, MWG in this example. Under Service Definition unselect the option to Auto Manage Addresses. Set the Proxy Type to Transparent For the To Service VLAN select 10.0.0.1 (VLAN 10.0.0.0). Click Add for HTTP Proxy Devices. Enter the MWG IP address, 10.0.0.55 in this example. Click Done. For the From Service VLAN select 10.1.1.1 (VLAN 10.1.1.0) Enable Port Remap. Set the Remap Port to 80. Set Manage SNAT Settings to Auto Map Click Save & Next at the bottom. Click the name of the Service Chain. Select the MWG Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the McAfee Web Gateway Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://10.4.11.52 Test this connection now and it should look like the following: In this example the MWG is configured with a Custom Category to block connections to http://10.4.11.99. When attempting to connect to this site with a web browser you should see a block page like the following: Conclusion This completes configuration of BIG-IP SSL Orchestrator with McAfee Web Gateway. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the MWG Service and inspected for malicious payloads or policy violations. Related Articles Integrating SSL Orchestrator with McAfee Web Gateway-Explicit Proxy Verified Design SSL Orchestrator with McAfee Web Gateway (Part 1) Verified Design SSL Orchestrator with McAfee Web Gateway (Part 2)4.2KViews3likes0CommentsIntegrating SSL Orchestrator with McAfee Web Gateway-Explicit Proxy
Introduction The Secure Sockets Layer (SSL) protocol and its successor, Transport Layer Security (TLS), are being widely adopted by organizations to secure IP communications. While SSL/TLS provides data privacy and secure communications, it also creates challenges to inspection devices in the security stack. What if attackers are hiding malware inside the encrypted traffic? An integrated F5 and McAfee Web Gateway solution solves the SSL/TLS challenges. F5 BIG-IP SSL Orchestrator centralizes SSL/TLS inspection. The decrypted traffic is then inspected by one or more McAfee Web Gateways, which can block previously hidden threats. This solution eliminates the blind spots introduced by SSL/TLS. Versions Tested This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 SSL Orchestrator version 11.0 McAfee Web Gateway version 11.2 McAfee Web Gateway will be configured as an Explicit Proxy Additional Help A demo video of this article is available below. If setting up SSL Orchestrator for the first time refer to the Deployment Guide availableHERE For information on SSL Certificate considerations and trust, click HERE McAfee Web Gateway (MWG) Configuration Configure the Explicit Web Proxy as follows Configure a Network Interface as follows Specify the IP address and mask to be used, 10.0.0.55 255.255.255.0 in this example. The Default Gateway will be the Self IP address SSL Orchestrator uses for explicit proxy connections, 10.0.0.1 in this example. BIG-IP SSL Orchestrator Configuration The BIG-IP VLAN settings should look like the following: 10.0.0.0 is the interfaces used for Explicit Proxy connections to the MWG North_vlan is used for network connectivity from the BIG-IP to the North South_vlan is used for network connectivity from the BIG-IP to the South The BIG-IP Self IPs setting should look like the following: 10.0.0.1 will be used for Explicit Proxy connections to the McAfee Web Gateway Note: in this example SSL Orchestrator is deployed with an L3 Outbound Topology. That’s what the other two Self IPs are for. Your configuration will look different if using an L2 Topology. This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration. Create the McAfee Web Gateway Service Under Services, click Add. In the Service Catalog select the Inline HTTP tab then double click on McAfee Web Gateway HTTP Proxy. Give it a name, MWG in this example. Under Service Definition unselect the option to Auto Manage Addresses. For the To Service VLAN select 10.0.0.1 (VLAN 10.0.0.0). Click Add for HTTP Proxy Devices. Enter the MWG IP address, 10.0.0.55 in this example. Set the port to 80. Click Done. Note: the McAfee HTTP Proxy port is specified in Configuration > Appliances > Proxies For the From Service VLAN select 10.0.0.1 (VLAN 10.0.0.0). Set Manage SNAT Settings to Auto Map Click Save & Next at the bottom. Click the name of the Service Chain. Select the MWG Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the McAfee Web Gateway Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://10.4.11.52 Test this connection now and it should look like the following: In this example the MWG is configured with a Custom Category to block connections to http://10.4.11.99. When attempting to connect to this site with a web browser you should see a block page like the following: Conclusion This completes configuration of BIG-IP SSL Orchestrator with McAfee Web Gateway. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the MWG Service and inspected for malicious payloads or policy violations. Related Articles Integrating SSL Orchestrator with McAfee Web Gateway-Transparent Proxy - DevCentral Verified Design: SSL Orchestrator with McAfee Web Gateway-Part 1 Verified Design: SSL Orchestrator with McAfee Web Gateway-Part 2 1.2KViews3likes0Comments
1.2KViews3likes0CommentsAutomating SSL Orchestrator in AWS with the help of Ansible and Terraform
Overview Learn how to automate the deployment of SSL Orchestrator in Amazon Web Services. This article is based on the automation templates available here: https://github.com/f5devcentral/sslo-cloud-templates This will deploy SSL Orchestrator with an L3 Inbound Topology and two L3 Services in a Service Chain. Follow the instructions here: lab-instructions-aws.md A demo video of this article is available below Steps Performed: Install the Container Environment Clone the Repository Subscribe to EC2 Instances Export your AWS Credentials Copy the Terraform variables file and update the values Deploy the Terraform configuration Build the SSL Orchestrator Topology using Ansible Deploy the Ansible Configuration Check the results Launch the development container environment Restart the container and attach to the console: Clone the Repository Subscribe to EC2 Instances From a web browser client - subscribe to the following EC2 instances: https://aws.amazon.com/marketplace/pp?sku=5e92658b-3fa7-42c1-9a9b-569f009582df https://aws.amazon.com/marketplace/pp?sku=78b1d030-4c7d-4ade-b8e6-f8dc86941303 https://aws.amazon.com/marketplace/pp?sku=a133064f-76e1-4d8a-aa3d-26ef12e6b95a Export your AWS Credentials From inside your development environment - export the AWS credentials export AWS_ACCESS_KEY_ID="your-aws-access-key-id" export AWS_SECRET_ACCESS_KEY="your-aws-secret-access-key" export AWS_SESSION_TOKEN="your-aws-session-token" Copy the Terraform variables file and update the values From the terraform-aws-sslo folder - Copy the includedterraform.tfvars.examplefile toterraform.tfvarsand update the values It should look like this: Deploy the Terraform Configuration From inside your development environment - deploy the Terraform configuration terraform init terraform validate terraform plan terraform apply -auto-approve Build the SSL Orchestrator Topology using Ansible Edit the ansible.cfg file and add the two lines at the bottom: [defaults] host_key_checking = False retry_files_enabled = False inventory = ./inventory/hosts library = ./library roles_path = ./roles collections_paths = ./collection [galaxy] server = https://old-galaxy.ansible.com cd ansible ansible-galaxy collection install f5networks.f5_modules f5networks.f5_bigip -f Deploy the Ansible Configuration Deploy an Ansible config using the variables file that was created by the accompanying Terraform. This will create an inbound layer 3 SSL Orchestrator topology. From the 'ansible' folder: cp ../terraform-aws-sslo/ansible_vars.yaml . ansible-playbook -e @ansible_vars.yaml playbooks/config-sslo-inbound-l3-complete.yaml Check the Results Login to the BIG-IP GUI and verify SSL Orchestrator has been configured and deployed Conclusion You're done! These templates and configuration files can be cusomized by you and re-used for future SSL Orchestrator deployments in AWS. 1.4KViews3likes0Comments
1.4KViews3likes0CommentsIntegrating SSL Orchestrator with Fortinet FortiGate Virtual Edition as a Virtual Wire
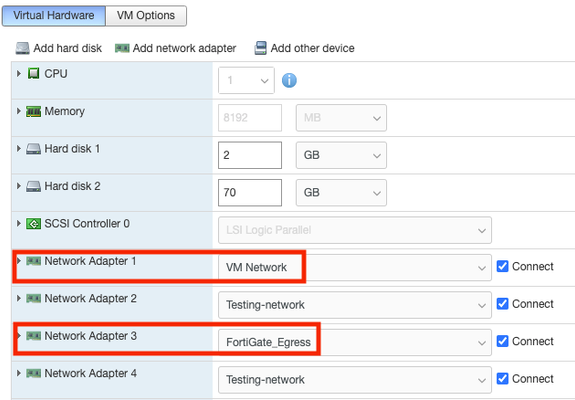
Introduction The Secure Sockets Layer (SSL) protocol and its successor, Transport Layer Security (TLS), are being widely adopted by organizations to secure IP communications. While SSL/TLS provides data privacy and secure communications, it also creates challenges to inspection devices in the security stack. What if attackers are hiding malware inside the encrypted traffic? An integrated F5 and Fortinet FortiGate solution solves the SSL/TLS challenges. F5 BIG-IP SSL Orchestrator centralizes SSL/TLS inspection. The decrypted traffic is then inspected by one or more Fortinet FortiGate VMs, which can block previously hidden threats. This solution eliminates the blind spots introduced by SSL/TLS. Prerequisites This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 F5 SSL Orchestrator version 11.0 Fortinet FortiGate Virtual Appliance Fortinet FortiGate version 7.2.4 Deployed on VMWare ESXi version 6.7 Fortinet FortiGate will be configured as a Virtual Wire in Transparent Mode Additional Help If setting up SSL Orchestrator for the first time refer to the Deployment Guide availableHERE For information on SSL Certificate considerations and trust, click HERE Demo video: Fortinet FortiGate Virtual Edition Configuration ESX Virtual Hardware Configuration The Network Adapters should be configured like the following: Network Adapter 1 is used for Management and corresponds to the “mgmt” interface on the FortiGate. Network Adapter 2 is used for egress connections from BIG-IP to port1 on the FortiGate. Network Adapter 3 is used for ingress connections from port2 on the FortiGate to BIG-IP. Create a Port Group for BIG-IP to connect to the FortiGate port1 interface. The ESX vSwitch topology should be configured as follows: Create a Port Group for BIG-IP to connect to the FortiGate port1 interface. The ESX vSwitch topology should be configured as follows: Fortinet FortiGate Configuration Enable Transparent Mode from the CLI. Configure the Virtual Wire as follows: Give it a name, vwire in this example. Add port1 and port2. Click OK. Create a Firewall Virtual Wire Pair Policy Select Policy & Objects > Firewall Virtual Wire Pair Policy > Create New Give it a name, “policy” in this example. Set the Source, Destination and Service. In this example they are set to all. The Action should be set to Allow. Optionally enable the Security Profiles. Click OK. F5 BIG-IP SSL Orchestrator VMWare ESXi Configuration Configure the Virtual Machine Network Adapters as follows: Network Adapter 1 is used for Management and corresponds to the management interface on the BIG-IP. Network Adapter 2 is used for network connectivity from the BIG-IP to the North. Network Adapter 3 is used for network connectivity from the BIG-IP to the South. Network Adapter 4 is used for egress connections from BIG-IP to port1 on the FortiGate. Network Adapter 5 is used for ingress connections from port2 on the FortiGate to BIG-IP. BIG-IP SSL Orchestrator Network Configuration The BIG-IP VLAN settings should look like the following: Egress is used for egress connections from BIG-IP to port1 on the FortiGate. Ingress is used for ingress connections from port2 on the FortiGate to BIG-IP. Network_North is used for network connectivity from the BIG-IP to the North. Network_South is used for network connectivity from the BIG-IP to the South. The BIG-IP Self IPs setting should look like the following: These Self IPs will be used for connectivity from the BIG-IP to the North and South. Self IPs are not needed for the connection from/to BIG-IP and FortiGate. Note: in this example SSL Orchestrator is deployed with an L3 Inbound Topology. That’s what the two Self IPs are for. Your configuration will look different if using an L2 Topology. BIG-IP SSL Orchestrator Configuration This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration. Create the Fortinet FortiGate Service Under Services, click Add. In the Service Catalog select the Inline L2 tab then double click on Generic Inline Layer 2 Give it a name, FortiGate in this example. Under Network Configuration click Add Under Network Configuration set From BIGIP VLAN to Egress. Set To BIGIP VLAN to Ingress. Click Done. Enable the Port Remap option to remap the port to 80. Click Save & Next at the bottom. Click the name of the Service Chain. Select the FortiGate Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the FortiGate VM. Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://192.168.0.5 Test this connection now and it should look like the following: A tcpdump taken from the BIG-IP Egress and Ingress VLANS should show the connection in plain-text HTTP: Conclusion This completes configuration of BIG-IP SSL Orchestrator with Fortinet FortiGate Virtual Edition. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the Fortinet FortiGate Service and inspected for malicious payloads or policy violations. Related Articles Integrating SSL Orchestrator with Fortinet FortiGate Virtual Edition1.3KViews2likes0CommentsIntegrating SSL Orchestrator with CheckPoint Firewall VM-Explicit Proxy
Introduction SSL Orchestrator centralizes & manages decryption of SSL/TLS traffic. This enables security and monitoring tools to view the decrypted content and analyze it for threats and other anomalies. SSL Orchestrator removes the burden of decrypting content from your security tools so they perform better and are more scalable. An integrated F5 and CheckPoint Firewall solution eliminates the blind spots introduced by SSL/TLS encrypted content. Versions Tested This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 SSL Orchestrator version 11.0 CheckPoint Gaia R81.20 CheckPoint SmartConsole version 81.20.9700.641 CheckPoint Firewall will be configured as an Explicit Proxy Additional Help If setting up SSL Orchestrator for the first time refer to the Deployment Guide availableHERE For information on SSL Certificate considerations and trust, click HERE Video demo VMware ESX Configuration Create the following 3 Port Groups: Network-North Network-South New-CheckPoint-Egress Attach them to a vSwitch, CheckPoint-Switch in this example: Configure the BIG-IP virtual network settings as follows: NOTE: VM Network is used for Management Network-North is used for connectivity to the North side of the network Network-South is used for connectivity to the South side of the network New-CheckPoint-Egress is used for connections from/to the BIG-IP and the CheckPoint Firewall Configure the CheckPoint Firewall virtual network settings as follows: NOTE: VM Network is used for Management New-CheckPoint-Egress is used for connections from/to the BIG-IP and the CheckPoint Firewall CheckPoint Firewall Configuration Using a web browser connect to the GAIA Portal. Under Network Management select Network Interfaces. In this example eth1 is being used for incoming and outgoing connections from/to the BIG-IP and the CheckPoint Firewall. It has an IP address of 10.0.0.5. NOTE: eth2 is not used in this example 10.0.0.5 will need a route or default gateway that is the BIG-IP Self IP of 10.0.0.1 (to be configured later). This example uses a closed network, a Static Route is added so the CheckPoint knows where to send connections destined for 192.168.0.5 (this is the IP address of the web server we will be using to test this). Launch the Smart Console and log in. Double click on the firewall you want to configure, check-fw1 in this example. Enable the HTTP/HTTPS Proxy with the following settings. Click OK when done. Double click on check-fw1 again. Select Network Management Select Get Interfaces then choose With Topology in this example. The Topology Results should look like the following. Click Accept then OK. NOTE: Typically eth1 (10.0.0.5) should be defined as Internal. Double click on the interface name to configure this. For eth1 click Modify. Set “Leads To” to Internal. Click OK Click Publish at the top. Click Publish again Click Security Policies on the left Change the Action from Drop to Accept NOTE: This is just an example for this article. Normally you would not set a firewall policy to Any/Any/Accept Select NAT and create a new NAT rule like the following: Set the Original Source to 10.0.0.1. Set the Original Destination to 10.0.0.5. Set the Translated Source to 10.0.0.5. Set Install On to the correct CheckPoint Firewall. Click Publish then Publish again When that completes click Install Policy Click Install NOTE: in this example the policy is installed on a single firewall. Your setup may differ. At this point the CheckPoint Firewall should be configured properly with an Access Control Policy and NAT BIG-IP SSL Orchestrator Configuration The BIG-IP VLAN settings should look like the following: Egress is the VLAN used for connections from/to the BIG-IP and the CheckPoint Firewall North_vlan is used for network connectivity from the BIG-IP to the North South_vlan is used for network connectivity from the BIG-IP to the South Create the following Self IP 10.0.0.1 is used for connections from/to the BIG-IP and the CheckPoint Firewall. The VLAN is set to Egress. This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration. Create the CheckPoint Firewall Service Under Services, click Add. In the Service Catalog select the Inline HTTP tab then double click on Generic HTTP Service Give it a name, CheckPoint in this example. Uncheck the box to Auto Manage Addresses. Set the Proxy Type to Explicit. For the To Service VLAN select 10.0.0.1/24 For HTTP Proxy Devices click Add Enter 10.0.0.5 for the IP Address. Enter 8080 for the Port. Click Done For the From Service select 10.0.0.1/24 Set Manage SNAT Settings to Auto Map. Click Save and Next. Click the name of the Service Chain. Select the CheckPoint Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the CheckPoint Firewall Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://192.168.0.5 Test this connection now and it should look like the following: We’ll use tcpdump on the BIG-IP to verify connectivity. The capture from the Network_South vlan shows the encrypted HTTPS request The capture from the Egress vlan shows plain text HTTP content being sent to the CheckPoint Firewall for Inspection NOTE: Some of the requests are identified as “webcache” due to using HTTP port 8080. Check the log file on the CheckPoint Firewall. Launch the SmartConsole and click LOGS & MONITOR. Double click on the entry highlighted below for more detail. Here we can see the connection was Accepted. We can also see the Service is http on TCP port 8080. Conclusion This completes configuration of BIG-IP SSL Orchestrator with CheckPoint Firewall. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the CheckPoint Service and inspected for malicious payloads or policy violations. Related Articles Integrating SSL Orchestrator with CheckPoint Firewall VM-Bridge Mode (L2) Integrating SSL Orchestrator with CheckPoint Firewall VM-Transparent Proxy - DevCentral1.4KViews2likes0CommentsIntegrating SSL Orchestrator with CheckPoint Firewall VM-Bridge Mode (L2)
Introduction SSL Orchestrator centralizes & manages decryption of SSL/TLS traffic. This enables security and monitoring tools to view the decrypted content and analyze it for threats and other anomalies. SSL Orchestrator removes the burden of decrypting content from your security tools so they perform better and are more scalable. An integrated F5 and CheckPoint Firewall solution eliminates the blind spots introduced by SSL/TLS encrypted content. Versions Tested This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 SSL Orchestrator version 11.0 CheckPoint Gaia R81.20 CheckPoint SmartConsole version 81.20.9700.641 CheckPoint Firewall will be configured in Bridging mode (L2) Additional Help If setting up SSL Orchestrator for the first time refer to the Deployment Guide availableHERE For information on SSL Certificate considerations and trust, click HERE Demo video: VMware ESX Configuration Create the following 4 Port Groups: Network-North Network-South New-Checkpoint-Egress New-Checkpoint-Ingress Attach them to a vSwitch, CheckPoint-Switch in this example: Configure the BIG-IP virtual settings as follows: NOTE: VM Network is used for Management Network-North is used for connectivity to the North side of the network Network-South is used for connectivity to the South side of the network New-Checkpoint-Egress is used for connections from BIG-IP to the CheckPoint Firewall New-Checkpoint-Ingress is used for connections from the CheckPoint Firewall to the BIG-IP Configure the CheckPoint Firewall virtual settings as follows: NOTE: VM Network is used for Management New-Checkpoint-Egress is used for connections from BIG-IP to the CheckPoint Firewall New-Checkpoint-Ingress is used for connections from the CheckPoint Firewall to the BIG-IP CheckPoint Firewall Configuration Using a web browser connect to the GAIA Portal. Under Network Management select Network Interfaces. Network interfaces cannot have an IP address when being added to a Bridge. In this example we’ll use eth1 and eth2. Click Add then select Bridge Set a Bridge Group number, 10 in this case. Add eth1 and eth2 to Chosen Interfaces. Click OK Launch the Smart Console and log in. Double click on the firewall you want to configure, check-fw1 in this example. Select Network Management Select Get Interfaces then choose one of the options, Without Topology in this example. The Topology Results should look like the following. Click Accept then OK. Click Publish at the top. Click Publish again Click Security Policies on the left Change the Action from Drop to Accept. Click Publish then Publish again When that completes click Install Policy Click Install NOTE: in this example the policy is installed on a single firewall. Your setup may differ. At this point the CheckPoint Firewall should be configured properly with a network Bridge and associated policy. BIG-IP SSL Orchestrator Configuration The BIG-IP VLAN settings should look like the following: Egress is the VLAN used for connections from BIG-IP to the CheckPoint Firewall Ingress is the VLAN used for connections from the CheckPoint Firewall to the BIG-IP Network_North is used for network connectivity from the BIG-IP to the North Network_South is used for network connectivity from the BIG-IP to the South Create the CheckPoint Firewall Service This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration. Under Services, click Add. In the Service Catalog select the Inline L2 tab then double click on Check Point Security Gateway Inline Layer 2 Give it a name, CheckPoint in this example, then click Add. For the To Service VLAN select Egress For the From Service VLAN select Ingress Click Done Enable Port Remap. Set the Remap Port to 80. Click Save and Next. Click the name of the Service Chain. Select the CheckPoint Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the CheckPoint Firewall Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://192.168.0.5 Test this connection now and it should look like the following: We’ll use tcpdump on the BIG-IP to verify connectivity. The capture from the Network_South vlan shows the encrypted HTTPS request The capture from the Egress vlan shows plain text HTTP content being sent to the CheckPoint Firewall for Inspection Conclusion This completes configuration of BIG-IP SSL Orchestrator with CheckPoint Firewall. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the CheckPoint Service and inspected for malicious payloads or policy violations. 1.1KViews2likes0Comments
1.1KViews2likes0CommentsF5 BIG-IP SSL Orchestrator Configuration with Advanced WAFaaS
Introduction This use case allows you to insert F5 Advanced WAF functionality in SSL Orchestrator from the Service Catalog. This is a new feature in SSL Orchestrator version 11.0. Note:This article applies to SSL Orchestrator version 11.0 and newer. If using an older version refer to the article HERE Below is a video demonstration of this article: Click HERE for a Lightboard Lesson on F5 Advanced WAF. Advanced WAFaaS is the ability to insert F5 BIG-IP Advanced WAF profiles into the SSL Orchestrator Service Chain for Inbound Topologies. This service allows you to configure and deploy Advanced Web Application Firewall profiles through the SSL Orchestrator. This configuration is specific to a WAF policy running on the SSL Orchestrator device. It is also possible to deploy WAF on a separate BIG-IP device, in which case you’d simply configure an inline transparent proxy service. The ability to insert F5’s Advanced WAF into the Service Chain presents a significant customer benefit. Some examples of the benefits are: Consolidation of best-in-class advanced WAF capabilities with SSL Orchestrator’s dynamic, policy-based decrypted malware inspection and traffic steering. The Advanced WAF Service can be used for multiple SSL Orchestrator Topologies. Management of SSL Orchestrator and Advanced WAF on the same platform. Simplifies logging and troubleshooting. This guide assumes you already have SSL Orchestrator and F5 Advanced WAF licensed and provisioned on the BIG-IP and wish to add this functionality to an Inbound Topology. In order to run Advanced WAF and SSL Orchestrator on the same device you will need an Advanced Web Application Firewall (AWF) add-on license. Note: SSL Orchestrator 11.0 requires BIG-IP version 17.1.0 Configuration From the SSL Orchestrator Guided Configuration click Services then Add Select the F5 tab then double click on F5 Advanced WAF (On-Box) Give it a name, F5_AWAF in this example Click the down arrow next to Application Security Policy and select your Advanced WAF policy, Advanced-WAF-Policy in this example The Advanced WAF Policy protects your web applications from application attacks like SQL injection, cross-site scripting and a variety of other malicious attacks. You can also specify a DoS Protection and Bot Defense Profile. A DoS Protection profile will also protect your web applications from Denial of Service attacks. A Bot Defense Profile will protect your web applications from malicious bot attacks Select a Log Profile if desired. The logging of connections is important for visibility and forensics. Click Save & Next at the bottom Click Save & Next at the bottom Click Deploy Click OK to the Success message Add the Advanced WAF Service to the Service Chain by clicking the Service Chains tab then click on the name of the Service Chain, Service_Chain in this example Move the F5_WAF Service from Available to Selected Click Deploy when done If presented with the following warning, click OK Click OK to the Success message When done it should look like the following The configuration is now complete. Using the F5 Advanced WAFaaS this way is functionally the same as using it by itself. There are no known limitations to this configuration. Additional Information For more information on configuration of SSL Orchestrator refer to the Deployment Guides HERE Exporting/Importing WAFaaS policy To export an existing Advanced WAF policy navigate to Security > Application Security > click the name of the policy you wish to export Click Export then choose one of the supported formats like XML To import the Advanced WAF policy click Create > Import from the Policies List screen Example of Advanced WAF Policy creation A demo video of Advanced WAF Policy creation is available HERE Example of Advanced WAF Protection in action SQL Injection is a common web application attack that should be blocked by the Advanced WAF policy. Here is what a typical SQL Injection attack might look like as an HTTPS request: https://10.1.20.200/rest/products/search?q=qwert%27%29%29%20UNION%20SELECT%20id%2C%20email%2C%20password%2C%20%274%27%2C%20%275%27%2C%20%276%27%2C%20%277%27%2C%20%278%27%2C%20%279%27%20FROM%20Users-- This request should be blocked and the response will look like this: Here is an example of what the Log File should contain: Note: Both Advanced WAF and SSL Orchestrator are CPU-driven functions. This will need to be factored into capacity planning when deploying the two together. 2.1KViews2likes0Comments
2.1KViews2likes0CommentsIntegrating SSL Orchestrator with Fortinet FortiGate Virtual Edition-Explicit Proxy
Introduction The Secure Sockets Layer (SSL) protocol and its successor, Transport Layer Security (TLS), are being widely adopted by organizations to secure IP communications. While SSL/TLS provides data privacy and secure communications, it also creates challenges to inspection devices in the security stack. What if attackers are hiding malware inside the encrypted traffic? An integrated F5 and Fortinet FortiGate solution solves the SSL/TLS challenges. F5 BIG-IP SSL Orchestrator centralizes SSL/TLS inspection. The decrypted traffic is then inspected by one or more Fortinet FortiGate VMs, which can block previously hidden threats. This solution eliminates the blind spots introduced by SSL/TLS. Prerequisites This article assumes you have SSL Orchestrator configured with a Topology and Service Chain F5 BIG-IP version 17.1 F5 SSL Orchestrator version 11.0 Fortinet FortiGate Virtual Appliance Fortinet FortiGate version 7.2.4 Deployed on VMWare ESXi version 6.7 Fortinet FortiGate will be configured as an Explicit Proxy Additional Help If setting up SSL Orchestrator for the first time refer to the Deployment Guide availableHERE For information on SSL Certificate considerations and trust, click HERE Demo video: Fortinet FortiGate Virtual Edition Configuration ESX Virtual Hardware Configuration The Network Adapters should be configured like the following: Network Adapter 1 is used for Management and corresponds to the “mgmt” interface on the FortiGate. Network Adapter 3 is used for Explicit Proxy connections and corresponds to the “port2” interface on the FortiGate. The other Network Adapters are not used. Create a Port Group for BIG-IP to connect to the port2 interface (Network Adapter 3) of the FortiGate. The ESX vSwitch topology should be configured as follows: Fortinet FortiGate Configuration Enable the Explicit Proxy feature. Configure the Explicit Web Proxy as follows Configure a Network Interface as follows Double click on Port2 to configure it Specify the IP address and mask to be used, 10.0.0.49 255.255.255.0 in this example. Enable the Explicit web proxy and click OK. A Static Route is needed for the Explicit Proxy connection. Configure it as follows: F5 BIG-IP SSL Orchestrator VMWare ESXi Configuration Configure the Virtual Machine Network Adapters as follows: Network Adapter 1 is used for Management and corresponds to the management interface on the BIG-IP. Network Adapter 2 is used for Explicit Proxy connections to/from the FortiGate. Network Adapter 3 is used for network connectivity from the BIG-IP to the North. Network Adapter 4 is used for network connectivity from the BIG-IP to the South. BIG-IP SSL Orchestrator Network Configuration The BIG-IP VLAN settings should look like the following: Network_North is used for network connectivity from the BIG-IP to the North. Network_South is used for network connectivity from the BIG-IP to the South. The BIG-IP Self IPs setting should look like the following: 10.0.0.1 will be used for Explicit Proxy connections to the FortiGate. Note: in this example SSL Orchestrator is deployed with an L3 Inbound Topology. That’s what the other two Self IPs are for. Your configuration will look different if using an L2 Topology. BIG-IP SSL Orchestrator Configuration This article assumes you have SSL Orchestrator configured with a Topology and Service Chain. Navigate to SSL Orchestrator > Configuration. Create the Fortinet FortiGate Service Under Services, click Add. In the Service Catalog select the Inline HTTP tab then double click on Fortinet Secure Web Gateway HTTP Proxy. Give it a name, FortiGate in this example. Under Service Definition unselect the option to Auto Manage Addresses. For the To Service VLAN select 10.0.0.1 (VLAN FortiGate_Egress). Click Add for HTTP Proxy Devices. Enter the FortiGate IP address, 10.0.0.49 in this example. Set the port to 8080. Click Done. For the From Service VLAN select 10.0.0.1 (VLAN FortiGate_Egress). Click Save & Next at the bottom. Click the name of the Service Chain. Select the FortiGate Service from the left and click the arrow to move it to the right. Click Save. Click OK Click Save & Next at the bottom. Click Deploy Click OK to the Success message. When done it should look like the following: From the Services screen if you expand the Pool Member Status you should see the FortiGate VM. Testing the Configuration In this example there is a Windows client that connects through the SSL Orchestrator to a Windows server running the following web site: https://192.168.0.5 Test this connection now and it should look like the following: In this example the FortiGate VM is configured with a Custom Category to block connections to http://192.168.0.99. When attempting to connect to this site with a web browser you should see a block page like the following: Note: in the block page you can see FortiGate VM has identified this site as HTTP and not HTTPS. This is because SSL Orchestrator has decrypted the HTTPS and sent the content to FortiGate as HTTP. Check the Security Dashboard on the FortiGate VM and you should see something like the following: Here you can see the attempt to access 192.168.0.99 is logged as a High Threat Level. Conclusion This completes configuration of BIG-IP SSL Orchestrator with Fortinet FortiGate Virtual Edition. At this point traffic that flows through SSL Orchestrator will be decrypted and sent to the Fortinet FortiGate Service and inspected for malicious payloads or policy violations. Related Articles Integrating SSL Orchestrator with Fortinet FortiGate Virtual Edition as a Virtual Wire990Views2likes0Comments