ASM Policy in "Blocking" Mode switch to "Transparent" for some IP's
I have a policy that I need to switch to blocking but the business want to have a phased approach. Only the testing team should be in Blocking, while the rest of the business (a different IP range) remains in transparent. I need to keep the same policy so that I can "proof" that everything is running fine. Is there a method to do that ? Was thinking about an iRule but dont know how. I know how to disable ASM with an iRule but, that's something I don't want because I need to keep the learning suggestions. Bye St.389Views0likes6CommentsF5 WAF/ASM block users that trigger too many violations by source ip/device id using the correlation logs
Hello to All, I was thinking of using the iRule tables command to write when a user ip/device id makes too many violations for a time perioud and to get blocked for some time but I see that the F5 ASM has correlation logs that trigger incidents but there is not a lot info if this can be used in iRules or to block user ip addresses / deviceid. https://support.f5.com/csp/article/K92532922Solved1.5KViews1like7CommentsBig-IP Next 20.2.0-2.375.1+0.0.43 iRule count problem
I have very simple iRule to show the problem: when HTTP_REQUEST { set Client_IP [IP::client_addr] if { ($Client_IP starts_with "x.x.x.x") && ([HTTP::uri] equals "/seed") } { table set -subtable TABLE "key1" "value1" 30 table set -subtable TABLE "key2" "value2" 15 table set -subtable TABLE "key3" "value3" 45 HTTP::respond 200 content "Done" TCP::close return } set key_value "key1" set key_value2 "key2" set key_value3 "key3" set count [table keys -subtable TABLE -count] HTTP::respond 200 content " Remaining timeout / defined timeout for ${key_value} => [table lookup -notouch -subtable TABLE ${key_value}] [table timeout -subtable TABLE -remaining ${key_value}]/[table timeout -subtable TABLE ${key_value}] Remaining timeout / defined timeout for ${key_value2} => [table lookup -notouch -subtable TABLE ${key_value2}] [table timeout -subtable TABLE -remaining ${key_value2}]/[table timeout -subtable TABLE ${key_value2}] Remaining timeout / defined timeout for ${key_value3} => [table lookup -notouch -subtable TABLE ${key_value3}] [table timeout -subtable TABLE -remaining ${key_value3}]/[table timeout -subtable TABLE ${key_value3}] Count TABLE ${count}" } It looks like table -keys -subtable <tablename> -count don't work properly: Remaining timeout / defined timeout for key1 => value1 27/30 Remaining timeout / defined timeout for key2 => value2 12/15 Remaining timeout / defined timeout for key3 => value3 42/45 Count TABLE 0 My expected output would be 3 (as it is not timeouted), not 0. Can someone check if I am correct? Or tell me how I can count not expired entries in table.95Views0likes4CommentsUri-based client cert authentication question
Hi, I need to configure a virtual server with selective client cert authentication based on URI. In case user select cert auth the uri changes to /myweb/secure/, F5 should request client cert, renegotiate SSL and insert client cert into HTTP header so the back-end server can read client cert. There is quite a lot of info and posts about this feature, which I've readed. I've config VS, SSL profile (client) and irule but I just can't make this work. SSL profile client: renegotiation enabled client authentication client certificate: ignore frequency: once trusted certificate authorities & advertised cert: bundle of client cert CA irule: when CLIENTSSL_CLIENTCERT { HTTP::release if { [SSL::cert count] < 1 } { reject } } when HTTP_REQUEST { if { [HTTP::uri] starts_with "/myweb/secure/" } { if { [SSL::cert count] == 0 } { HTTP::collect SSL::authenticate always SSL::authenticate depth 9 SSL::cert mode require SSL::renegotiate } } } when HTTP_REQUEST_SEND { clientside { if { [SSL::cert count] > 0 } { HTTP::header insert "x-clientcert" [X509::whole [SSL::cert 0]] } } } I'm not sure whether /myweb/secure/ path is ever accesible, since there is no browser pop-up requesting the client certificate. I really can't figure this out, any hints would be most appreciated. Thanks a lot for your time and help.176Views0likes1CommentiRule for Logging a HTTP::header
Hello, we have a VS that services multiple FQDNs to one VS and then chooses the pool using an LTM policy that checks the incoming http host from the client and then associates to the pool. I have a working irule that looks like: when HTTP_REQUEST_RELEASE { foreach x [HTTP::header names] { log local0. "$x: [HTTP::header $x]" } } the problem is, this returns all the headers for every HTTP_request for this VS, for ALL The FQDNs, when i really only need it for one specific one. I know in the header there is a Host field for the fqdn. is there a way to modify my irule above to only log the header for the HTTP::headers that contain the url lets say webserverA.com? Note: I tried to do the logging in the LTM policy for when it chooses the WebserverA pool, but while it says it accepts TCL, I don't know what to put in there.Solved46Views0likes1Commentapm session variable from part of uri...
Hey all, I have a problem I need to solve. We have an application that uses a mobile app, the app does authentication with apm(local sp/external idp) through one browser and then accesses the the backend server in another session.. and the apm is not aware of that second one so it gerenrates a new login which fails and the app cannot login. The app passes a identification value the the urls which the app uses.. I want to do the same. Does anyone know or have any tips on how i can catch part of the uri (sort of like this https://test.com/sessionid=1234-5678-9101) that contains the sessionid and apply it to a session variable? /Kim47Views0likes3CommentsF5 iRules Akamai redirection
Hello Team, Currently, i have a virtual server with iRules of redirection if my url start with /toto redirect to pool_test1. However, my problem is with AKAMAI every time when i request a http request "mycompany.com" i'm redirecting to /toto without any explanation. Have you a suggestion please to fix this issue ? Thank you.383Views0likes5CommentsAPM inactivity timeout redirect or notification page for LTM + APM connections
Background on this: Have a customer that is publishing a Microsoft CRM instance behind APM and doing KCD with smart card auth. Access policy works fine, KCD works fine, web app works fine. The only problem we have is the inactivity timeout setting. Once the limit has been reached, the session is removed and content is no longer sent to the user in a very abrupt fashion. This is a problem because ALOT of the page is cached on the clients workstation and all they see is broken JPEGs and incomplete web content. Once they click around they are re authenticated but it is not pretty. I want to find a way to notify the user they have been inactive for a certain amount of time, send a HTTP 200 response with content notifying them with a link to click on to re authenticate. The option of increasing the inactive timeout is not an option due to their access session license limit. There would be alot of abandoned sessions that would aggregate potentially going over this limit. I know with webtop and ssl vpn, you get a notification that you are about to be logged out due to inactivity but this doesn't seem to be available for LTM + APM policies. This is what I have so far, there has to be a more efficient way of doing this though. when ACCESS_SESSION_STARTED { set ::EXPIRE "false" } when ACCESS_SESSION_CLOSED { log local0. "Session has been closed" set ::EXPIRE "true" } when HTTP_RESPONSE { if {$::EXPIRE equals "true"} { HTTP::respond 200 content " You've Been Logged out due to inactivity You have been logged out due to inactivity Thanks for Using the application Click to log back in. " } }698Views0likes3Commentsempty character in policy conditions
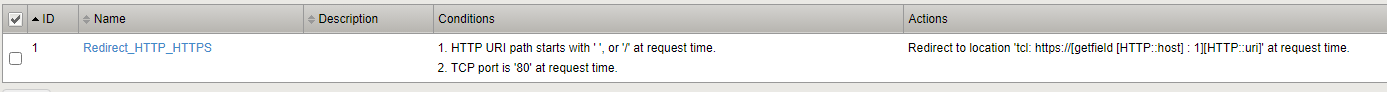
Hello good, I have changed iRule to policies, I have an HTTP-->HTTPS redirection rule that is formed as follows. when HTTP_REQUEST { if { ( [HTTP::uri] equals "" ) or ( [HTTP::uri] equals "/") } { HTTP::redirect https://[getfield [HTTP::host] ":" 1][HTTP::uri] } According to that iRule, whether the uri begins with / or ' ', it redirects me to HTTPS But when it comes to passing it to policies, I can't find the way to indicate the empty character. Does anyone know how to indicate it? I have already tried to put ' ' and add it but it doesn't work. Greetings and thanks.20Views0likes1CommentiRule to replace content of the location header on HTTP Responses
I'm trying to create an iRule that will detect if a web server is sending it's private IP address in the location header on it's responses. The logic is to read the location header in the responses, detect if the private IP addresses of the servers are included on them and replace the content of the location header to the website's URL, leaving everything else intact. This is the initial code I came up with. Should this work? Any better suggestions? when HTTP_RESPONSE { if { ( [HTTP::header Location] contains "10.0.0.11" ) || ( [HTTP::header Location] contains "10.0.0.12" ) } { [HTTP::header Location] replace "www.mywebsite.com" } }1.7KViews0likes3Comments