Sending HSL data in json format.
Just wanted to know if data can be sent via HSL in json format as below : HSL::send $hsl "{ "Attacker_IP":$remoteip, "Destination_IP":[IP::local_addr], "User-Agent":$useragent, "ISP":$isp, "Country":$country, "Original_Domain":[HTTP::host], "Original_URI":[HTTP::uri], "Fully_decoded_URI":$decodedUri, "Timestamp":$timestamp, "XFF_Header":[HTTP::header X-Forwarded-For]}" Is there some other way to achieve this?Solved1.3KViews0likes6CommentsDevice Fingerprinting for mobile devices
We have published Microsoft Exchange server behind ASM+APM policies. I am using BotDefense to generate Device IDs for the connecting clients and then inserting the value of "device_id" variable into HTTP header and then passing it to APM. APM extracts the "device_id" value from HTTP header and sets it as an APM variable: ACCESS::session data set "session.custom.device_id" "$device_id" This APM session variable is then called in APM iRules to perform the required logic. So far, the logic and traffic flow is working as expected. Now, here comes the problem part: If the client is not a web browser, the whole logic fails because BotDefense is generating Device IDs based on JavaScript challenge. In case of Microsoft Exchange, the client could be a mobile device using the native email app of the phone (not mobile browser) like the mail app of Andriod or iOS devices. How can we perform device fingerprinting and generate Device IDs in such case? All mobile devices use the standard Exchange protocol "Microsoft ActiveSync" which is based on HTTPS. When traffic hits my virtual server from a mobile client, BIG-IP can detect it and differentiate it from other web browser traffic because all requests coming from mobile devices have this particular URI string in the HTTP Request: "/Microsoft-Server-ActiveSync". But because it is not a web browser, the JavaScript challenge is not performed and no Device ID generated. My question is: How can we perform fingerprinting and generate Device IDs for mobile devices (not mobile browsers)? Here is my ASM iRule which is handling the Device IDs and fingerprinting: ============================================================================================================================== when RULE_INIT { set static::TPS_Value 1 set static::debug 1 # set as 1 - send request logs set 0 if no request logs should be sent. set static::PBD_debug 1 # list of botdefense actions you want to get request log on set static::Logged_PBD_actions "tcp_rst browser_challenge internal_bigip_response captcha_challenge" set static::host_header "Host: webmail.company.com" } when HTTP_REQUEST { set hsl [HSL::open -proto TCP -pool ASM_Log_Pool2] set http_request [HTTP::request] #HSL::send $hsl $http_request } when BOTDEFENSE_REQUEST { #for demo purpose, make the challange valid from the first request - make sure you go to the default if {[HTTP::uri] equals "/"} { BOTDEFENSE::cs_allowed true } #Mandate the device_id attribute extraction BOTDEFENSE::cs_attribute device_id enable } when BOTDEFENSE_ACTION { set device_id [BOTDEFENSE::device_id] if {$static::debug > 0} {log "reason is, [BOTDEFENSE::reason], action is [BOTDEFENSE::action], botdefense device_id is: $device_id"} if {$static::Logged_PBD_actions contains [BOTDEFENSE::action]} { set botdefense_action [BOTDEFENSE::action] set botdefense_reason [BOTDEFENSE::reason] set PBD_header [concat Host: webmail.company.com\r\nPbd_Action: $botdefense_action\r\nPbd_reason: $botdefense_reason] set asm_http_requet_log [string map -nocase [list $static::host_header $PBD_header] $http_request] if {($static::PBD_debug > 0) && ([info exists asm_http_requet_log])} { HSL::send $hsl $asm_http_requet_log } } log "action is [BOTDEFENSE::action], reason is: [BOTDEFENSE::reason] cs_allowed is: [BOTDEFENSE::cs_allowed]" if {([BOTDEFENSE::action] eq "tcp_rst") && [BOTDEFENSE::cs_allowed] eq 0} { set res [BOTDEFENSE::action custom_response { sorry i am blocking you, try to restart the session } 200] if {$res eq "ok"} { set botdefense_responded 1 } } #if {[BOTDEFENSE::action] eq "captcha_challenge"} { #set res [BOTDEFENSE::action allow] #log "captcha challange with res $res" #if {$res eq "ok"} { #log "bypass allow" #} #} #} when ASM_REQUEST_DONE { if {$static::debug > 0} {log "http uri is [HTTP::uri]"} virtual Hackazone_APM_virt } when HTTP_REQUEST_SEND { clientside { # Need to force the host header replacement and HTTP:: commands into the clientside context # as the HTTP_REQUEST_SEND event is in the serverside context if {$static::debug > 0} {log "device id is: $device_id"} HTTP::header insert "device_id" "$device_id" #if { $suspicious_browser eq "1" } { #HTTP::header insert "suspicious_browser" "1" #log "sending suspicious_browser header" #} #log "after the change [HTTP::request]" } } when HTTP_RESPONSE_RELEASE { if {[info exists botdefense_responded]} { HTTP::header insert "X-TS-BP-Action" "2" } } =================================================================================================================================== Many thanks.773Views1like1CommentBigIP DNS Log queries
Hello We have GTM only licensed VM And we'd like to log all the queries to either the local system to remote syslog But neither ways are working Not sure if this matters but I'd like to mention that we're using GTM as cache forwarded zone, and if no domain match there then it falls to the default pool attached to the listener So back to logging, we tried two ways: local-db--publisher , but not sure where to find all queries logs?... remote hsl to to kiwi server but also there no logs been sent I simply what to see queries logs ... how should i accomplish this task?702Views0likes2Commentsalertd high cpu usage
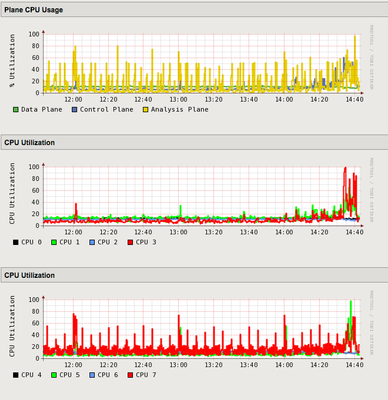
Hello, So we tried taxing the HSL logging of our 12.1.2 cluster with several (4) simple while true; do curl http://virtual-ip/; done curl loops. The virtual IP had a simple iRule that logged [HTTP::request] several times. Our logging is BSD syslog to HSL, to a logstash pool. During our testing, we saw alertd rising to 100% CPU and maxing out there. CPU usage on the dashboard increased aswell, as you see in the image below. sys log-config destination remote-high-speed-log elk-hsl-destination { pool-name syslog-pool } sys log-config destination remote-syslog rsyslog-to-hsl-elk { remote-high-speed-log elk-hsl-destination } sys log-config filter elk-hsl-filter { level info publisher elk-hsl-publisher } sys log-config publisher elk-hsl-publisher { destinations { rsyslog-to-hsl-elk { } } } Any idea how we can combat this? We would like to use HSL to reduce CPU consumption, but this seems like a lot of fuss for simple logging. Ideas? Thanks!Solved622Views0likes1CommentMost efficient methods for Connection logging?
Does anyone have real world experience with logging connections at a high rate? If so, which methods are you using to collect and transmit the data? We have a requirement to log all connections going through our F5 devices. Things like the client/server-side IPs/ports as well as HTTP details for HTTP VIPs and DNS details from our GTMs. It's the Whitehouse M-21-31 mandate if anyone if familiar with it. I've used Request Logging Profiles and various iRules with HSL to collect this type of data before, but I've never been too concerned about overhead because I would only apply them as needed, like when t-shooting an issue with a VIP. Our busiest appliance pushes around 150k conn/sec and 5k HTTP req/sec, so I now have consider the most efficient methods to avoid any kind of impact to traffic flows. I've done some lab testing with several different methods but I can't do any meaningful load tests in that environment.Below are some of my opinions based on my lab testing so far. Data Collection AVR - I like that this single feature can meet all the requirements for collecting TCP, HTTP, and DNS data. It would also be relatively easy to perform audits to ensure the VIPs have the necessary Analytics profiles as we can manage it from the AVR profiles themselves. My main concern is the overhead that results from the traffic analysis. I assume it has to maintain a large database where it stores all the analyzed data even if we just ship it off to Splunk. Even the data shipped off to Splunk includes several different logs for each connection (each with a different 'Entity'). Request Logging Profile- This is fairly flexible and should have low overhead since the F5 doesn't need to analyze any of the data like AVR does. This only collects HTTP data so we still need another solution to collect details for non HTTP VIPs. It would be a pain to audit since we don't have use any kind of deployment templates or automation. iRule - This provides a lot of flexibility and it is capable of collecting all the necessary data, but I don't know how well performance overhead compares to AVR. This would also be a pain to audit due to lack of deployment templates and automation. Data Transmission HSL UDP Syslog- I imagine this is the most efficient method to send events, but it's likely only a matter of time before we are required to use TCP/TLS. Telemetry Streaming - This is the more modern method and it offers some interesting features like System Poller, which could eventually allow us to move away from SNMP polling. We would need a workaround for our GTM-only devices because they cannot run a TS listener.615Views0likes1CommentKnown limitation of HSL with proc
Hi, We have iRules in which we log using HSL. If log servers are down we log locally. We wanted to convert HSL logging to proc so that instead of writing these many lines of code just for logging we can use a proc. Is there any known of using HSL with proc. when CLIENT_ACCEPTED { set hsl [HSL::open -publisher $static::log_publisher] if { $log_hsl == 1 } { if {[active_members hsl_pool] < 1 ] } { log local0.info "Accepted client conn [IP::client_addr]:[TCP::client_port]" } else { HSL::send $hsl "$CLIENT_ACCEPTED_INFO Accepted client conn [IP::client_addr]:[TCP::client_port]" } } else { log local0.info "Accepted client conn [IP::client_addr]:[TCP::client_port]" } } Thanks Syed Nazir522Views0likes5CommentsHigh-Speed Logging Mgmt Interface
I am trying to setup high-speed remote logging on my Big-IP ASM v12.1.1. I have gone through the f5 documents setting up the server pool, then log destination/publisher/filter, but am not getting any logs. I just read on a post that high-speed logs won't be sent over the mgmt interface. Is that true? Will i need to setup another interface (with static routes?) just for the high-speed logging?485Views0likes3CommentsHSL request logging profile, requests not showing in logs, how to improve reliability?
How "reliable" is the HSL logging profile capability? Is it known that there may be requests that do not get logged, because of the F5 not sending the UDP packet? Or, if there are requests not being logged, is basically definite that the UDP packets are being dropped, either at the network level or by the log collector (Kiwi syslog server, if it matters)? We have a specific data flow that involves two layers of F5 load balancing: Client -> F5-1 -> F5-2 -> real server We have an HSL request logging profile in place for the VIPs on both F5s. With perfect logging, we would expect to see a 1:1 ratio of requests hitting F5-1 and F5-2 - but we don't, we see many logged requests hitting F5-2 without a corresponding request logged on F5-1. We know for a fact that those requests did come through F5-1, because on F5-2 we log both the client-ip and X-Forwarded-For header, and can see F5-1 the client-IP, and both the original client IP and the F5-1 in the XFF header. In trying to identify the root cause of the missing log messages, are there any logs on the F5s that would indicate if logging is failing, or a rate has been exceeded, or any other kind of issue? We do only have 1 log collector in the associated pool - but the request rate is pretty low, only about 10-15 requests/second; and if that server were being overwhelmed, we would expect to see even drops, not mostly/all F5-1's messages being dropped. In terms of trying to improve reliability, would switching to TCP be advised? Any other suggestions, for either locating the issue, or improving reliability? Thank you!480Views0likes1Comment